Table of Contents Hide
- 1 What is Internet of Things
- 2 What Exactly Does IoT Do
- 3 IoT Architecture
- 4 Data Flow
- 5 IoT Platform
- 6 IoT Device
- 7 Computing and Storage
- 8 IoT Gateway
-
9
Communications and Networking
- 9.1 Application layer
- 9.2 Transport layer
- 9.3 Internet layer
- 9.4 Network layer
-
10
IoT Applications
- 10.1 Smart wearables
- 10.2 Smart cities
- 10.3 Smart homes
- 10.4 Smart manufacturing
- 10.5 Smart agriculture
- 10.6 Smart healthcare
- 10.7 Smart transportation

The world has never been so connected with the Internet and smartphones, yet a new wave of technological revolution is profoundly changing the way that people relates to the environment around and interacts with everything associated. Interweaving the physical world with the digital realm through networked sensors, actuators, embedded hardware and software, Internet of Things (IoT) opens up a host of possibilities that produce massive benefits across all aspects of our lives. The evolving and expanding IoT ecosystems are set to provide contextual services, unlock new operational insights, facilitate resource management, and maximize revenue growth. IoT has rapidly taken center stage in business and consumer world with a converged infrastructure dedicated to connection, computing and data harvesting across the entire IoT stack.
What is Internet of Things
IoT refers to an ecosystem in which applications and services are driven by data and insights generated by Internet-connected devices that sense and interface with the physical world. In other words, IoT is the extension of the Internet into the physical world. In this cyber-physical system, devices (physical things) with context-awareness and communication capabilities are connected to the Internet (cyberspace) to deliver advanced analytics and actionable reports through software-based applications. The seamless integration of sensing technologies, networking connectivity, computing power, machine learning, analytical approaches and software platforms creates a hybrid construct, which revolutionizes data acquisition for planning and decision-making. With cloud computing and big data analytics being ubiquitously employed to offer a nearly endless source of business and informational insight, Internet of Things is poised to be the catalyst that drive innovations in every sector.What Exactly Does IoT Do
In a nutshell, IoT was born to optimize our living and working environment by automating the processing and retrieval of data and leveraging machine intelligence to maximize the value of data assets. It takes advantage of the widespread communications and network infrastructure to enable full, convenient, and intelligent control over the entire cyber-physical system.Remote operation
The very nature of IoT emphasizes the network connectivity of smart devices thus making them controllable from a remote location. Computer software programs with web-based user interfaces and mobile apps provide application level capabilities for humans to monitor, configure and program smart devices virtually anywhere in the world as long as there's Internet connection.Sensing and detection
IoT is founded on the digitalization of the variations in environments. It interfaces with the physical world via sensors and detectors which quantitatively measure the physical phenomena or characteristically identify the presence of an object and convert the detected variations into electrical signals for subsequent analysis and management.Interconnection and interoperation
IoT goes far beyond simple point-to-point device control as well as centralized management of multiple nodes. The ecosystem accommodates all types of smart devices designed with different functionalities but speaking a universal language of network communication. These devices can interoperate to create a robust IoT environment capable of solving complex tasks. IoT systems typically implement a distributed mesh networking architecture in which network nodes are interconnected and can talk with each other, in such a way, to create a system with no points of failure.Efficient resource management
The IoT architecture is typically run on a centralized cloud-based service which provides scalability for managing physical and digital resources across multiple deployments. Intelligent analytics optimize workflows and processes while machine learning delivers new operational insights to unlock opportunities for maximum cost reductions and efficiency improvement. The intelligent, intuitive IoT platform drastically reduces time-consuming manual efforts even on project management with an enormous scale of connected environments.Task automation
The ultimate goal of IoT is to automate complex tasks through machine intelligence and cognitive technologies such as machine-to-machine interaction (M2M), artificial intelligence (AI), swarm intelligence (SI), machine learning, and augmented reality (AR). Advanced algorithms can be programmed to create triggers which are set to be activated in different scenarios. The incredible potential of IoT will be released through high volumes of data streams. Over time IoT systems become smarter and smarter.IoT Architecture
The IoT architecture may be viewed as a framework that defines the layers of an IoT stack, specifies the physical components of a network, and establishes a hierarchical model annotated with logic that determines the actions to be taken on events for each layer. There is no single consensus on a standardized architecture for IoT. The most basic architecture is a three-layer IoT stack comprised of the perception, network, and application layers.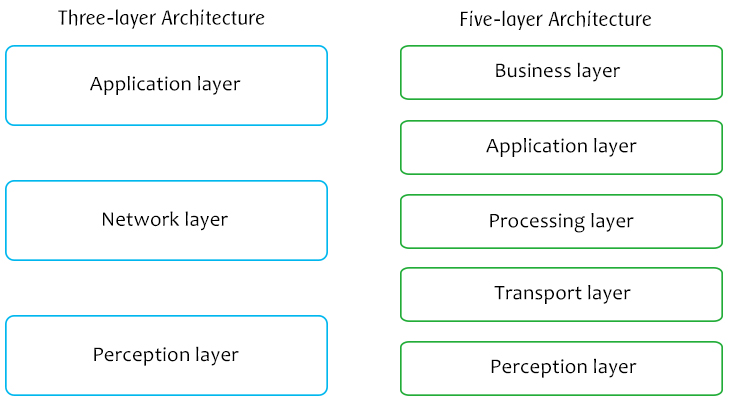
Conceptual three- and five-layer IoT stacks
The perception layer is the physical layer where all the data and information are gathered by data collection devices. These devices are typically designed as embedded systems that consist of microprocessors/microcontrollers, sensors or actuators, memories, communication modules and interfaces. Depending on the type of sensors, devices working in this layer can provide information about temperature, location, orientation, movement, vibration, acceleration, humidity, etc.
The network layer, also known as the transmission layer, handles the addressing, routing and processing of the data collected from the hardware infrastructure to other smart things, network devices, and servers. Network layer is the infrastructure to provide wireless or wired network communications.
The application layer, which is considered as a top layer of conventional IoT architecture, provides IoT content retrieval, data management, and access control. This layer provides practical applications in which the Internet of Things can be deployed based on end-user applications, e.g. smart home, smart city, smart health, intelligent agriculture, smart retail, intelligent transportation, etc.
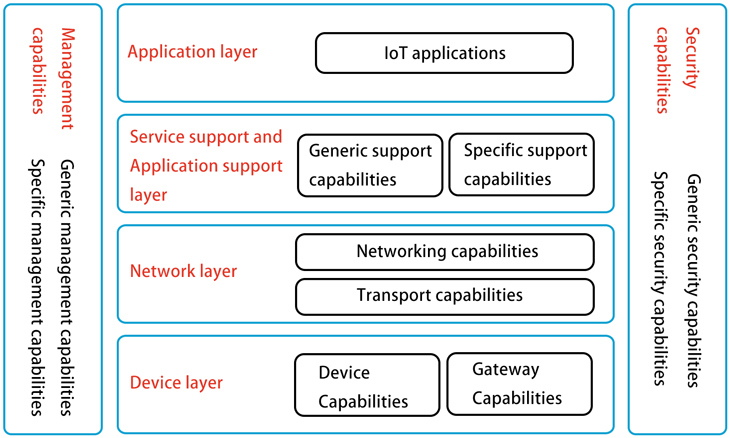
IoT reference model by the International Telecommunication Union
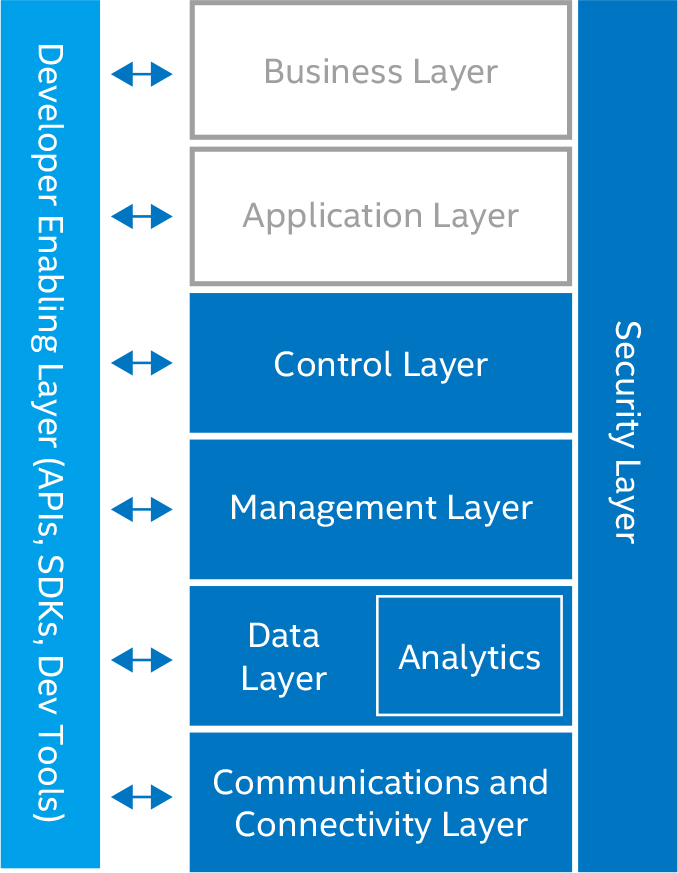
The three-layer architecture is just a conceptual IoT stack that is far from feasible for commercial IoT deployments. More layered architectures have been proposed for building a more sustainable, scalable, secure, and mobile IoT ecosystem. The five-layer architecture is another abstract yet more practical IoT architecture which additionally includes the processing and business layers. These five layers are perception, network, processing, application, and business layers. The role of the perception and application layers remains the same as in the three-layer architecture. The network layer, or more commonly known as the transport layer in the five-layer architecture, is responsible for data transmission only. The data processing role is taken over by the dedicated processing layer which is also called the middleware layer. This layer stores, analyzes, and processes data using various tools and technologies such as databases, cloud computing, and big data. The business layer which manages the whole IoT system builds business models and graphs that help determine future actions and business strategies.
The business and application layers are user or services layers. The functional layers from data collection to data processing are the major runtime layers, which have a wide variation among different applications and architecture proposals. For example, the runtime layers may include an edge (fog) computing layer which executes codes in the IoT gateways or the devices. Most often, a security layer is vertically embedded into all layers on the stack to enable secure, end-to-end solutions. Many IoT architectures have a developer enabling layer (APIs, SDKs, developer tools) that allows IoT solutions and applications to be tailored at various layers.
Intel IoT Reference Architecture
Data Flow
A typical data flow through an industrial IoT architecture starts from data sensing and identification. Endpoint sensing devices (IoT devices) convert analog signals to digital signals using an analog-to-digital converter (ADC). Data is collected by a gateway and relayed to a data center or network server via standard IP connections. Gateways are designed to provide bidirectional communication between the data center and IoT devices. The data center, which ingests sensor data and implement data analytics applications, provides real-time responses (control commands) to the gateways. The digital control signals which are forwarded to the IoT devices by the gateway are converted into analog signals using a digital-to-analog converter (DAC). The new analog input will be responded by actuators, motors, solenoids and relays.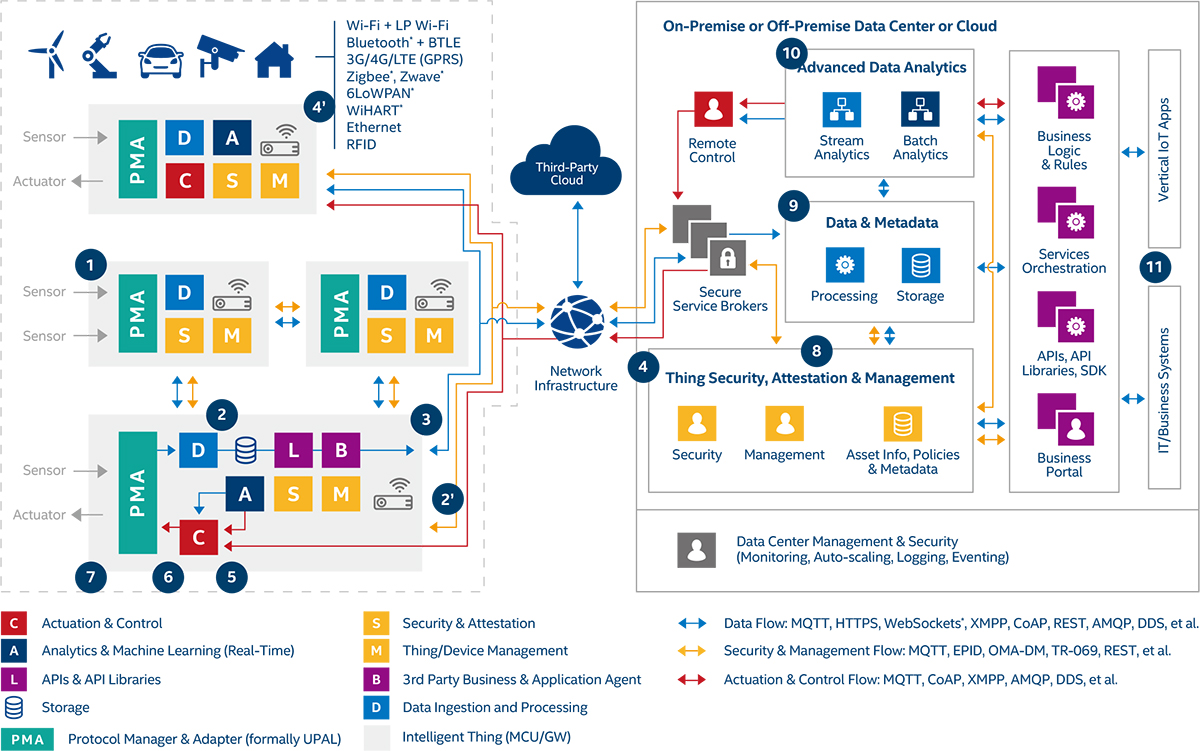
Intel IoT's Data Flow for Devices without Native Internet Connectivity
IoT Platform
An IoT platform is an end-to-end software framework that handles connection and information exchange between IoT devices and IoT applications. It comprises of a suite of software components designed to orchestrate the movement of data between IoT devices and various connected environments while facilitating a full complement of data analytics capabilities. The platform streamlines data ingestion, data storage, data governance, data analysis, and data visualization to unlock new operational insights and fuel better business outcomes. Edge technologies, big data processing and analytics, and machine learning create value-added, data-enabled services out of massive volumes of heterogeneous, streaming and geographically-dispersed real-time data. It secures the IoT system by providing functions such as authentication, authorization, data encryption, security monitoring, identity and access management. A robust IoT platform provides scalability, extensibility and interoperability between heterogeneous devices and their business models to facilitate reliable machine-to-machine communication and support a variety of programming approaches that match developer preferences.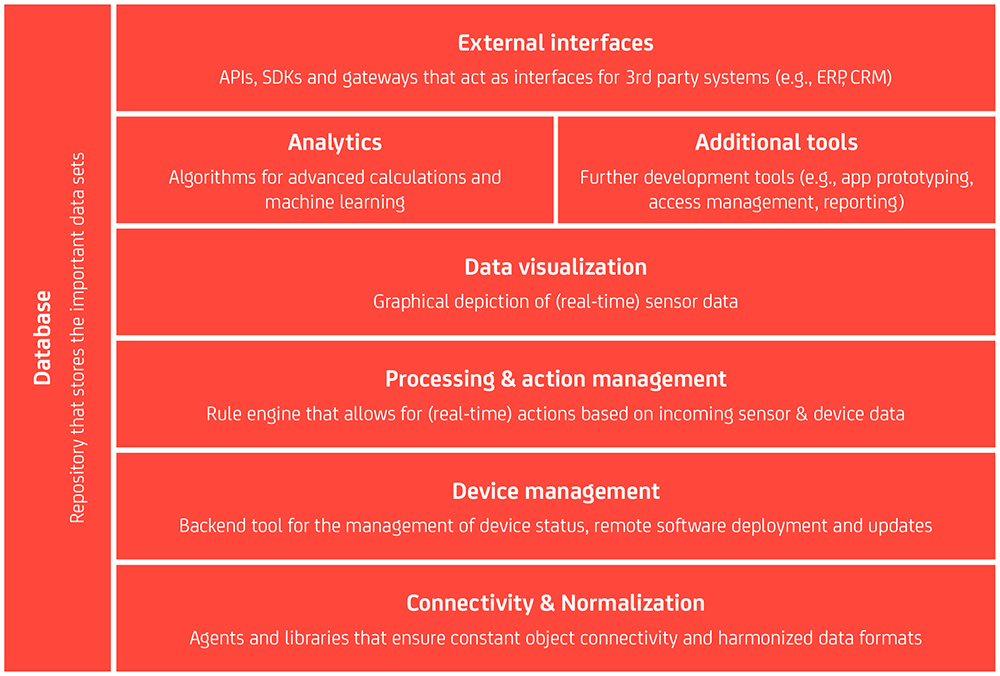
The eight major building blocks of an IoT platform (Source: IoT Analytics)
IoT Device
An IoT device is an embedded system that is context aware to a targeted environment. IoT ecosystems are built on devices that provide sensing, actuation, identification, control, and monitoring activities. IoT devices use sensors to measure or detect certain characteristics of the physical world and convert the value of a physical parameter into an electrical signal. There are array of sensing devices, which includes motion sensors, flow sensors, temperature sensors, voltage sensors, humidity sensors, leak detectors, smart thermostats, intelligent streetlights, water monitors, fitness trackers, acoustic transducers, etc. The actuator in an IoT device operates in the reverse direction of a sensor. It turns a digital command into physical action. An IoT device has a microcontroller or microprocessor which provides local control for sensors and actuators. The smart device also include Read Only Memory (ROM) to stores the microcontroller's software program and Random Access Memory (RAM) to store and receive data. An IoT device must have network connectivity so that it can communicate with external control, such as an IoT gateway, as well as other IoT devices within the network. The embedded system has remote management capabilities and supports a device management protocol. The firmware contained in devices provides the low-level control program for the devices.Computing and Storage
As IoT devices are usually unable to store and process the massive amount of data generated in real-time, most data is forwarded to the data center, often a cloud-based solution. Cloud is given primacy because it offers an effective, pervasive, dynamically provisioned platform to store, streamline and analyze big data. The architecture of cloud computing provides scalability and elasticity to handle varying data volume, velocity, and related processing requirements. However, there are numerous scenarios where latency goes far beyond any acceptable levels. Low-latency communication is thus vital for time sensitive, mission-critical IoT applications such as assisted driving, robotic control for industrial automation, and remote surgery.The addition of edge (fog) computing addressed the bottlenecks of cloud computing by having data crunching and analytics move closer to the data source. In a fog computing model, data analytics and knowledge generation occur in an edge computing device, such as a gateway device. Fog computing significantly decreases the data volume that must be transmitted between end devices and cloud. By shifting intelligence from a core centralized cloud to the edge of an IoT system, end users no longer have to struggle with latency issues.
IoT Gateway
An IoT gateway is a network interface device that links the IoT devices at the edges of the network to a core network infrastructure. The gateway provides bidirectional communication, relaying messages between edge devices and the remote IoT platform. Gateways ingest data, execute commands, and support multicast operation. It establishes secure wireless connections with multiple edge devices via a built-in radio module and connects to the network server via standard IP connections. A field gateway performs local processing, control functions and protocol normalization. It can filter or aggregate device telemetry and thus allows data processing and independent applications to run at the edge of the network to minimize latency. A cloud gateway allows data to flow to and from IoT devices through one or multiple application-level messaging protocols. It offers a brokered communication model to support event-driven architectures. The cloud gateway provides transport-protocol-level connection management while protecting the communication path, device authentication, and authorization toward the system.Communications and Networking
IoT is all about two-way data communications in an interconnected and interoperable network of physical devices. Any IoT solution counts on reliable communications and robust connectivity to thrive. The IoT communication model goes beyond the Internet Protocol (IP) communication as IoT has diversified communication models which include device to device, device to cloud, device to gateway, and cloud to cloud. To leverage IoT to its full potential, the challenges such as communication quality (bandwidth, latency) and security, network stability and reliability, and power constraints must be addressed. Many protocols have been developed for network communications in different IoT layers.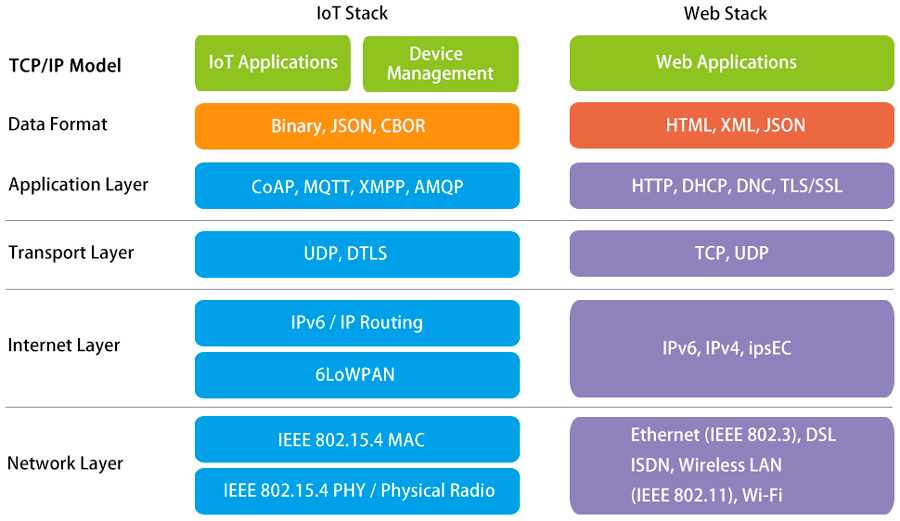
Application layer
The Constrained Application Protocol (CoAP) is a specialized web transfer protocol that implements the REST (Representational State Transfer) communication paradigm that powers today's web services. The web friendly protocol allows the manipulation of resources identified by Uniform Resource Identifiers (URIs), which makes machine-to-machine (M2M) communication natively compatible to the Internet. CoAP comes with a lightweight binary header and support for multicast operations over UDP which uses a simpler approach to TCP with less overhead.Message Queue Telemetry Transport (MQTT) is a publish/subscribe protocol that runs over TCP and thus requires open connection channel. The lightweight messaging protocol is designed for constrained nodes such as sensor motes or small embedded devices with flaky network connectivity, low computing power, and connections where bandwidth is at a premium. CoAP offers a brokered communication mode, therefore it can hold or queue messages for observers and is capable of coordinating subscriptions and also authenticating the client for security.
Transport layer
Transmission Control Protocol (TCP), widely known as Internet Protocol (IP), is a connection-oriented communication protocol. TCP uses a three-way handshake to create reliable connections across a network. This core protocol of the Internet protocol suite runs on a plethora of packet switching network systems the most popular of which is the Ethernet. It provides a mode connected service to the upper layers and supports acknowledgment, retransmission and flow control. However, TCP is not a good protocol for communication in low power environments because its large overhead can be overkill.Universal Datagram Protocol (UDP) is a packet-based protocol that is used to transport units of data called datagrams over an IPv4 or IPv6 network. Compared to TCP's default header size of 20 bytes, UDP has a simpler and shorter 8-byte header. This translates to less energy for packet transmission and reception, more space for application data, and small code footprint, making it well-suited to real-time data applications with low reliability demand, such as voice and video broadcast. However, there is no provision of recovery mechanism for lost packets and no mechanism is available for splitting application data into appropriate packet sizes.
Datagram Transport Layer Security (DTLS) is the security protocol for datagram-based communication and authentication in IoT environments. Based on the stream-oriented TLS protocol, DTLS provides end-to-end security for CoAP which runs over the inherently and intentionally unreliable UDP. DTLS, however, does not support multicast communication.
Internet layer
6LoWPAN, an acronym for IPv6 over low power wireless personal area networks, is an IP based, IoT-oriented network designed to interoperate with any solution based on IEEE 802.15.4 networks. 6LoWPAN provides IPv6 (and UDP) header compression, packet fragmentation and reassembly, as well as an adaptation layer between standard IP data packets (1280 bytes) and the IoT optimized packets of 802.15.4 (127 bytes). Packets sent from the Internet can be seamlessly transmitted across an 802.15.4 link and vice versa. 6LoWPAN supports unicast and broadcast, autoconfiguration for neighbor devices discovery, conversion between IPv4 and IPv6, and ciphered transportation using AES 128 (and AES 64 for constrained devices). 6LoWPAN networks connect to the Internet via a gateway which translates compressed IP v6 addresses to ensure bidirectional communication between the Internet and IoT nodes.
Network layer
This layer provides connectivity between endpoints and exchange data streams through the network at the electrical, optical, or radio level. Various communication protocols and technologies thrive in this layer.Long range IoT radio solutions
NB-IoT, which uses a subset of the 3GPP LTE global standard, offers long range, low power, low data rate, high availability, high security and managed M2M communication. NB-IoT creates a star wireless network, allowing devices to be deployed in the field without using a gateway device. This feature, along with its ability to operate RF-resistant environments such as buildings and below-ground installations such as subways, offers NB-IoT an advantage for large scale citywide deployment wherein high installation speed is a necessity. This narrow band IoT solution has the least power consumption of any cellular IoT standard and can achieve battery life of more than 10 years. NB-IoT is supported by all major mobile equipment, chipsets, and module manufacturers, which allows this technology to co-exist and interoperate with 2G, 3G, and 4G mobile networks. Both NB-IoT and LTE-M, another licensed spectrum solution, are integrated in the 5G specifications.LTE-M, also referred to as LTE Cat-M1 or enhanced Machine Type Communication (eMTC), is a similar evolution of 3GPP to NB-IoT. LTE-M eliminates the need for full-featured LTE devices reducing device (modem) complexity while still providing cellular-quality coverage. As with NB-IoT, this Subscriber Identity Mod-ule (SIM)-based technology enjoys the security benefits that major carrier networks offer. LTE-M devices take advantage of extended Discontinuous Repetition Cycle (eDRX) and Power Saving Mode (PSM) techniques. These power management features allow the IoT devices to have longer sleep cycles while the modem remains connectable. The narrow band radio solution also has interoperability with existing deployment.
LoRa (short for Long Range) is a Low Power Wide Area (LPWA) networking technology that uses CSS (Chirp Spread Spectrum) modulation at its physical layer. Spread spectrum modulation allows it to tread data rate for sensitivity within a fixed channel bandwidth and provide orthogonal separation between signals. CSS modulation not only enables data transmission at long range and low power, but also yields advantages of adaptive data rate, scalable bandwidth, high-power efficiency, multipath resistance, and robustness against interference. LoRa operates in sub-GHz bands including 433 MHz and 863–870 MHz in Europe, 902–928 MHz in the US, and 915–928 MHz in Australia. Sub-GHz band operation alleviates LoRa from experiencing attenuation and multipath fading caused by obstacles and dense surfaces such as concrete walls. LoRaWAN is a Media Access Control (MAC) layer protocol that uses LoRa technology at the physical layer to manage communication between endpoint devices and LPWAN gateways.
Sigfox is an ultra-narrow band (UNB) LPWAN solution which is designed to handle low data rates of 10 to 1,000 bps using a DBPSK modulation scheme. It offers an excellent option for applications where there is requirement of exchanging small quantities of data without frequent communication. Sigfox nodes use a Random Frequency and Time Division Multiple Access (RFTDMA) to access randomly in time and frequency to the wireless medium without any contention-based protocol. Each gateway can handle up to a million of connected objects with very long-range connectivity (up to 30km in rural areas and 3–10 km in urban) between the base station and the node using a star network topology. However, its downlink frequency band is severely limited (869.40 - 869.65 MHz) and there may arise an issue with signal interference.
Ingenu is another proprietary LPWA radio technology that uses a patented Random Phase Multiple Access (RPMA) scheme for uplink transmissions. Ingenu provide secure LPWAN solutions at 2.4 GHz band and transmits at data rates in the hundreds of thousands of bits per second. It is capable of effective bidirectional transmission under the most challenging RF environments and requires fewer access points than cellular, LoRa, and Sigfox. The Ingenu protocol itself supports low latency applications and provide enterprise level security with 256-bit encryption and two-way authentication. However, Ingenu networks have a power consumption higher than Sigfox and LoRa.
Short range IoT radio solutions
ZigBee is an open, global wireless standard designed to provide a complete connectivity solution with excellent device interoperability and cloud connectivity. ZigBee leverages the IEEE 802.15.4 physical layer and operates in unlicensed radio bands including 2.4 GHz for smart home applications, 915 MHz in US and Australia, 868 MHz in Europe and 784 MHz in China. The self-healing, secure, robust, and mesh-capable networking protocol uses Carrier Sense Multiple Access with Collision Avoidance (CSMA-CA) and spread spectrum communications to enable multihop routing and ensure performance in multipath, noisy, and low signal strength RF environments. ZigBee's RF range is usually between 10 and 30 m although its theoretical range can be up to 100 m. ZigBee utilizes the header compression techniques of 6LoWPAN to reduce the communication overhead and improve the overall network performance.Z-Wave is a proprietary, low energy RF technology for wireless communications in sub-GHz bands, including 900 MHz range, 868 MHz in Europe and 908 MHz in the United States. Z-Wave employs a simple protocol and consumes extremely low amounts of power. The protocol is optimized for reliable, low latency communications. A Z-Wave mesh network supports up to 232 devices, which include controllers and slaves. Z-Wave routes its messages through the network using a Source Routing Algorithm (SRA) so that a message initiator device can compute the best route for messages to travel and generate a complete route through the mesh network to the recipient. Z-Wave devices communicate at 40Kbp/s, with a range of approximately 30 m.
Thread is an IPv6-based mesh networking protocol that runs on top of the well-known radio standard IEEE 802.15.4 operating at 250Kbps in the 2.4GHz band. The low-power protocol implements an IPv6 addressing architecture that comes with 6LoWPAN header compression and mesh capabilities for maximum routing efficiency and redundancy. Thread supports full mesh connectivity between all routers in the network without the need for custom software. Thread's multi-hop wireless networking capability allows signals to reach their destination by traveling through multiple relay points. The Thread network supports up to 250 nodes (with a limit of 32 active routers). All Thread networks are AES encrypted to provide security at the network, transport and application layers.
Bluetooth Low Energy (BLE) is a short-range solution developed to use about half the energy of Classic Bluetooth while providing greater performance, range, privacy and security enhancements. BLE operates in the 2.4GHz ISM band and uses 40 2MHz-wide channels. With both payload and overhead kept under very strict limits, Bluetooth has been optimized for low latency transmission of large amounts of very small packets. Bluetooth takes an adaptive frequency-hopping spread spectrum (AFHSS) scheme to combat the frequency-static interference. BLE also offers generic attribute (GATT) profiles which allow applications to communicate and/or request data stored in structures that defines the services, characteristics and attributes of a given node. BLW also has a beaconing function offered by no other solution. Beacons are tiny short-range transmitters that can be utilized to provide location-based services. Latest Bluetooth implementations offer mesh networking capability which is crucial for the large scale deployments in which IoT devices may span vast areas. Bluetooth 4.0 has a maximum speed of 25 MB/second and a distance of 60 m. Bluetooth 5.0 has a range of up to 243 m and a maximum data rate of 50 MB/second.
Wi-Fi or Wireless Fidelity is a massively successful Wireless Local Area Network (WLAN) family of communication standards that operates in two modes, ad-hoc mode (peer-to-peer) or infrastructure mode (peer-to-AP). Wi-Fi technology defines the physical layer and the data link layer of a local network. This IEEE 802.11 family of standards include 802.11a operating in the 5 GHz band, 802.11b and 802.11 g operating in the 2.4 GHz band, 802.11n operating in the 2.4/5 GHz bands, 802.11ac operating in the 5 GHz band, 802.11ad operating in the 60 GHz band, and 802.11ah operating in the 900 MHz band. The high-bandwidth communication standard, which supports high bandwidth, multimedia streams and very large file transfers with a communication range of up to 20 m (indoor) and 100 m (outdoor), is the de facto standard for transmitting large amounts of data across a wireless network. Nevertheless, Wi-Fi is extremely power intensive and has a strong impact on the battery drain. A long battery life is critical in the resource-scarce IoT world. Wi-Fi HaLow which is based on the IEEE 802.11ah standard, consumes less power than a traditional Wi-Fi device while reaching twice the range of traditional Wi-Fi standards. Wi-Fi HaLow is intended to compete Bluetooth in IoT applications for smart homes, connected cars, industrial applications, and smart cities.
Li-Fi or Light Fidelity is a short-range wireless communication technology that uses light waves to transmit data. Li-Fi networks employ a modem that modulates the light to transpose electrical signals into light signals. This high-speed modulation is imperceptible to the human eye. A Li-Fi enabled IoT device has a photodetector which converts the light signals back to an electrical signals. Li-Fi is considered as an appealing IoT application since it easily converts ubiquitously available LED lamps and luminaires into access points capable of receiving and transmitting data. It occupies the band from 380 nm to 750 nm in the electromagnetic spectrum which is 10,000 times larger than the RF spectrum. This fundamentally addresses the bandwidth limitations than challenge RF applications. Unlike RF applications which are prone to interference and attenuation, Li-Fi does not interfere with other RF electromagnetic signals. Moreover, Li-Fi is intrinsically safe as it does not create electromagnetic interference (EMI). However, this technology is currently struggling with providing an efficient uplink scheme.
Very-short range IoT radio solutions
Radio frequency identification (RFID) is an automatic identification technology that uses radio waves to read or write information stored on passive, semi-passive or active RFID tags. The basic architecture of an RFID system consists of RFID tags, RFID readers and data processing stations. RFID systems can be classified into Low Frequency (LF) systems that operate in 30–500 KHz, High Frequency (HF) systems that operate in 10–15 MHz, and Ultra High Frequency (UHF) systems that operate in 850–950 MHz, 2.4–3.5 GHz and 5.8 GHz. RFID technology has long been employed in data acquisition applications such as inventory and asset management, access control, and product tracking. RFID connects physical objects to the Internet, making it an indispensable contributor to a variety of IoT applications.Near field communication (NFC), an extension of RFID technology, enables devices positioned in close proximity (within distance from 4cm to 10cm) to one another to share information. NFC operates on the carrier frequency of 13.56 MHz and has a maximum data rate of 424 kbps. There are three operation modes of NFC: Card Emulation Mode that enables NFC-enabled devices to act like smart cards, Reader/Writer Mode for detecting and reading information stored on external, NFC-compatible tags, and Peer-to-peer mode that enables data exchange and file shareing between two NFC-enabled devices.
Wired
Ethernet over Fiber (EoF) and Ethernet over Copper (EoC) created local area networks (LANs) with high communication reliability and high data transport capacity over larger distances. Since the IEEE Standard 802.3 was published to harmonize specifications for the physical and lower software layers of wire-bound Ethernet networks, computer networking technologies has since continued to evolve to accommodate intelligent building applications. Power over Ethernet (PoE), an access layer technology that uses standard Ethernet cable to deliver low voltage power to devices, offers intriguing contrasts with wireless approaches for IoT applications. By eliminating the need for separate network and power wiring installations, PoE facilitates the introduction of M2M devices within buildings and maximizes the energy savings from connected LED lighting systems.
Power line communication (PLC) network leverages power grid infrastructure as communication medium. PLC networks can be divided into narrowband (125 Hz –500 KHz) and broadband (1.8–100 MHz) networks which allow date rates up to 100 kbps and beyond 2 Mbps, respectively. Most PLC systems operate by adding a modulated carrier signal to the wiring system using OFDM technique at physical layer. PLC is severely challenging for transporting communication signals because power cables were not custom-made for data communication. High impedance, noise and attenuation can deteriorate system performance when it comes to achievable throughput, bit-error rate (BER), latency, signal-to-noise ratio (SNR).
IoT Applications
With computing brought into the physical world and ubiquitous smartphone apps and wireless connectivity supporting data flowing through interconnected systems, the potential value across consumer-oriented and business-to-business (B2B) IoT applications is limited only by the imagination. The rapid progress in machine-to-machine interaction (M2M), artificial intelligence (AI), machine learning (ML) and augmented reality (AR) facilitates the IoT transformations.





























































































































